Crypto exchanges don’t fail because of weak marketing, they fail because they lose trust. From high-profile hacks to regulatory crackdowns, the lesson is consistent: when security standards aren’t built into the foundation, confidence evaporates overnight and recovery is nearly impossible.
The rulebook has become clearer. Exchanges entering the market today are expected to meet five essential security standards that cover custody, governance, compliance, access protection, and solvency. These aren’t nice-to-have checkboxes; they are the minimum criteria regulators, institutions, and increasingly informed users use to decide which platforms they can rely on.
1. CCSS (CryptoCurrency Security Standard) – Custody Discipline
The CryptoCurrency Security Standard (CCSS) was developed to address a critical blind spot. While global frameworks like ISO/IEC 27001 govern information security and PCI DSS governs payment card data, neither captured the unique risks of crypto key management where a single private key compromise can wipe out billions. CCSS closes this gap by establishing technical and operational rules specifically for wallets, keys, and transaction authorization.
For exchanges, custody is not just another security layer, it’s the heart of the business. In 2022, Chainalysis reported that $3.8 billion in crypto was stolen, with more than 80% of losses tied to poor custody practices in exchanges and DeFi platforms. CCSS directly addresses these vulnerabilities with requirements such as:
- Secure key generation and storage using deterministic random bit generators (DRBGs) and offline entropy sources to prevent predictable keys.
- Multi-signature or Threshold Signature Schemes (TSS) so no single insider or compromised key can move funds independently.
- Hardware Security Modules (HSMs) for tamper-resistant key storage and execution.
- Audit logging and penetration testing to expose misuse or anomalies in real time.
- Proof-of-Reserves validation, ensuring solvency claims are cryptographically verifiable.
But CCSS is not just a technical checklist, it is also a certification process that validates implementation rigor.
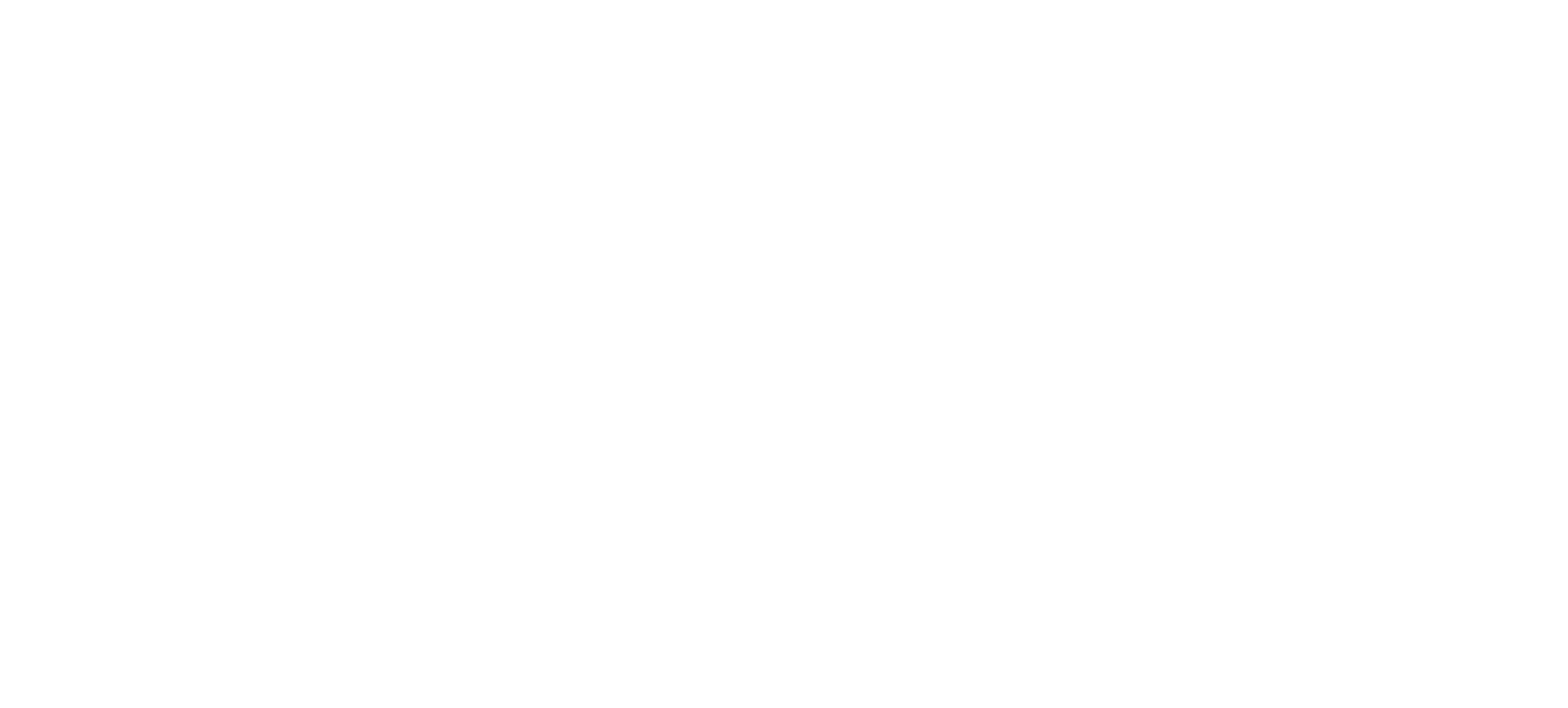
CCSS audit and certification workflow for exchanges. (Source: CryptoCurrency Certification Consortium)
The CCSS audit process requires independent review, peer validation, and certification before an exchange can publicly claim compliance.
This certification pathway is what turns CCSS into a market signal. For instance, WhiteBIT’s achievement of CCSS Level 3 demonstrated to regulators and institutional partners that its custody operations were resilient even against insider collusion and advanced attacks. For new exchanges, pursuing CCSS compliance is no longer a branding exercise, it’s a gateway to institutional trust, regulatory acceptance, and long-term credibility. For additional context, see navigating exchange listing standards in 2025.
2. ISO/IEC 27001 – Governance of Information Security
If CCSS secures custody, ISO/IEC 27001 ensures exchanges have governance across the entire information ecosystem. It goes beyond technology, requiring an Information Security Management System (ISMS), a framework that forces leadership to identify risks, implement controls, monitor them continuously, and improve over time.
For exchanges, this translates into:
- Documented policies for access control, incident response, and disaster recovery.
- Independent auditing to prove that practices exist in reality, not just on paper.
- Executive accountability for risk management, not just delegated to IT teams.
- Continuous monitoring of vulnerabilities and threats instead of ad-hoc patches.
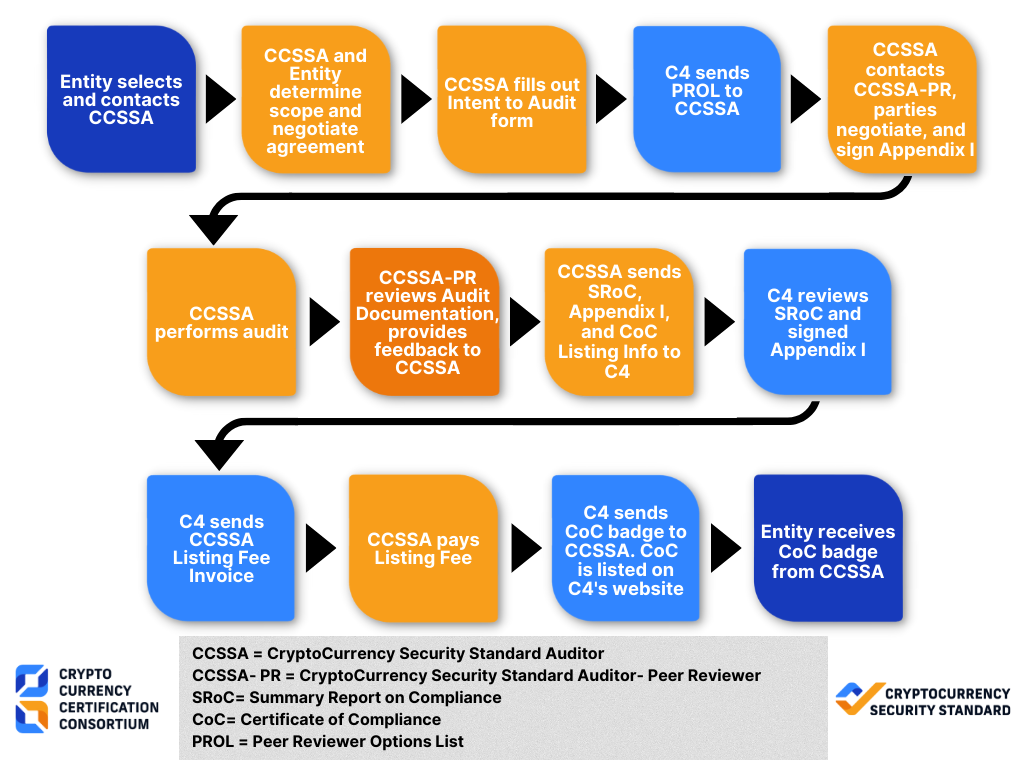
The standard itself is evolving to keep pace with the threat landscape. The 2022 revision streamlined Annex A controls, cutting the number from 114 to 93 and regrouping them into 4 broader domains instead of 14. New controls were also added for cloud use, threat intelligence, and secure coding practices—areas directly relevant to exchanges that rely heavily on APIs and third-party providers.
SO/IEC 27001:2022 revisions overview (Source: Robere & Associates Indonesia)
The 2022 revision modernized ISO/IEC 27001 by reducing and reorganizing controls, and adding new requirements for cloud and coding security critical areas for exchanges.
Globally, more than 70,000 organizations hold ISO 27001 certification across financial services, tech, and cloud industries. When exchanges like Gemini and Coinbase publicize ISO 27001 compliance, they aren’t just signaling IT hygiene, they are showing regulators and institutions that they operate with the same governance discipline as banks. For new exchanges, adopting ISO 27001 doesn’t just reduce risk; it signals maturity and builds credibility with the institutional partners they need to grow.
3. FATF Travel Rule & KYC/AML – Compliance Baseline
No matter how strong the custody or technology, an exchange without compliance collapses fast. Regulators worldwide now treat AML (Anti-Money Laundering) and KYC (Know Your Customer) controls as the foundation of exchange legitimacy. At the core of this is the FATF Travel Rule, which obliges Virtual Asset Service Providers (VASPs) to transmit verified sender and recipient details with every qualifying transaction.
In practice, this means exchanges must:
- Verify customer identities before transactions can be processed.
- Share originator and beneficiary data securely between VASPs.
- Sanctions screen both parties to block blacklisted individuals or entities.
- Perform counterparty due diligence to ensure other VASPs meet regulatory standards.
- Decide whether to accept or reject transactions based on compliance outcomes.
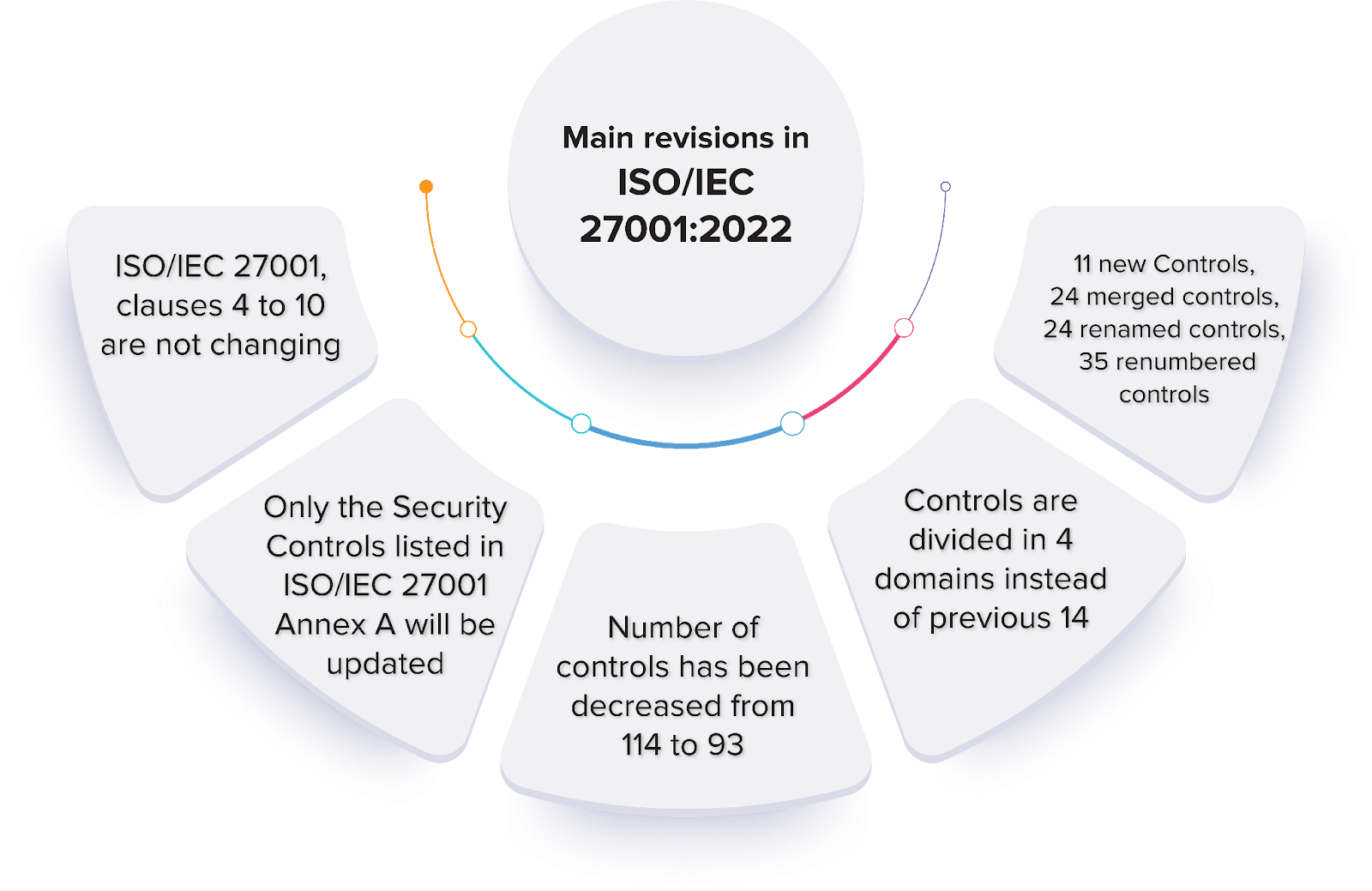
FATF Travel Rule information-sharing process between VASPs (Source: Nota Bene)
The FATF Travel Rule requires VASPs to verify both sender and recipient, exchange details, screen for sanctions, and assess counterparties before approving a transaction.
This is more than paperwork. In the EU, MiCA mandates licensing, disclosures, and reserve requirements. In the U.S., the SEC’s cybersecurity rules demand incident reporting and board-level oversight. In Singapore, MAS licensing requires ongoing AML/CFT frameworks.
The cost of failure is heavy: Binance was fined over $4 billion in 2023 for AML violations, the largest penalty in crypto history. For new exchanges, compliance is not simply about avoiding fines, it’s what enables access to banking partners, fiat rails, and institutional clients. Without it, exchanges are excluded from the financial system entirely.
4. API and Access Security Standards – Protecting the Entry Points
Every exchange interaction user logins, order submissions, liquidity APIs flows through application programming interfaces (APIs). They are the lifeblood of trading systems, but also the attack vector most often exploited. A single leaked API key can lead to instant fund outflows, making API defense not just an IT concern but a core exchange security standard.
Modern exchanges are expected to adopt a layered stack of recognized API security protocols:
- OAuth 2.0 and PKCE (Proof Key for Code Exchange) for delegated authorization that prevents token theft during login flows.
- JWTs (JSON Web Tokens) for integrity-protected session management, reducing the risk of tampering.
- HMAC (Hash-Based Message Authentication Codes) and X.509 certificates to verify message authenticity and secure client–server communication.
- MFA (Multi-Factor Authentication), now industry baseline for both retail users and admin accounts.
- CORS (Cross-Origin Resource Sharing), SAML, and OIDC to harden identity federation and cross-domain integrations.
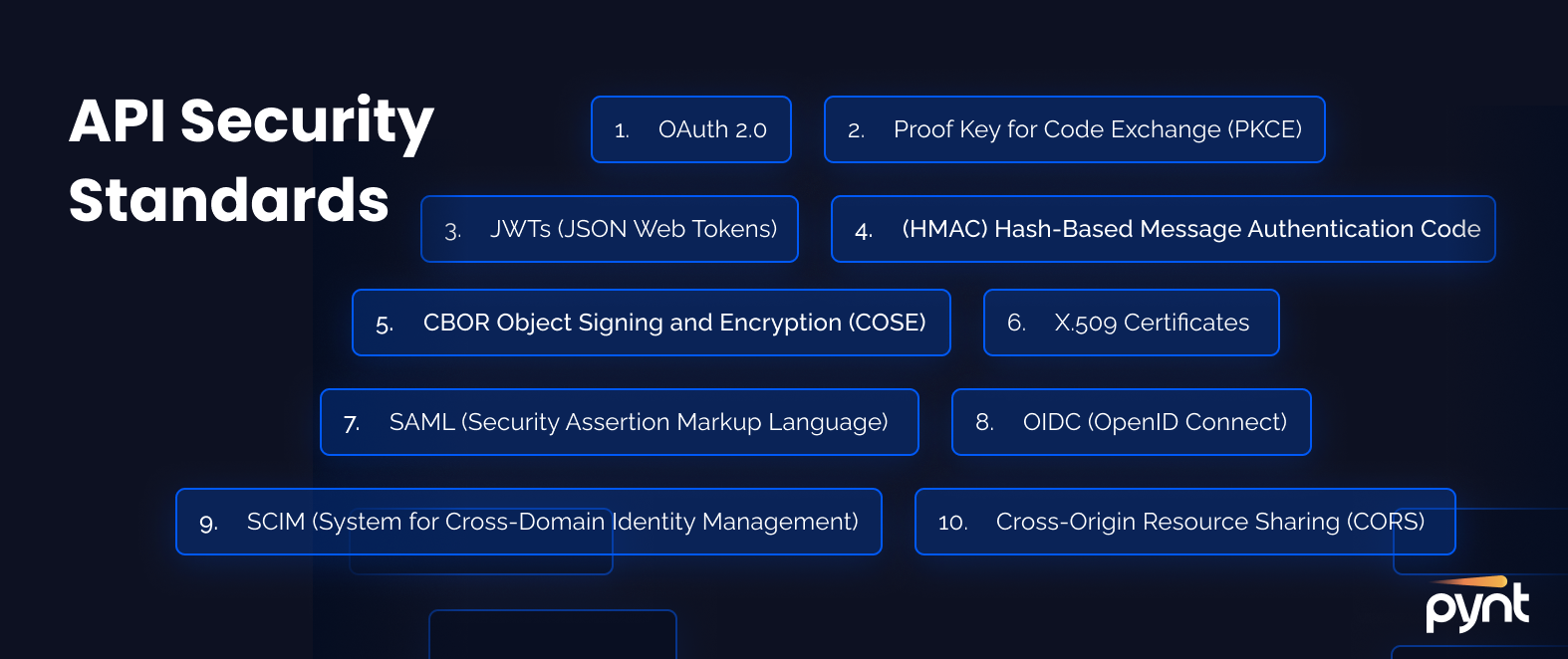
API security standards including OAuth 2.0, JWT, PKCE, HMAC, and others (Source: Pynt)
Modern exchanges are expected to enforce a stack of API security protocols to protect logins, session integrity, and data transfers.
The stakes are high. IBM’s Cost of a Data Breach Report 2023 found that compromised credentials accounted for 16% of breaches worldwide, with average costs surpassing $4.45 million per incident. For exchanges, where compromised API keys can lead directly to drained hot wallets, the damage can be instant and irrecoverable.
Industry leaders respond with continuous penetration testing, real-time anomaly detection, and IP whitelisting for institutional clients. This isn’t optional hygiene exchanges that fail to implement API standards face not only higher breach risks but also rejection from partners and regulators. In practice, secure APIs are now a prerequisite for institutional onboarding and fiat integration.
5. Proof-of-Reserves and Operational Resilience – Transparency Under Stress
The collapse of FTX proved that even exchanges with large trading volumes can implode if reserves are hidden, overstated, or inaccessible. Proof-of-Reserves (PoR) has since become a defining security requirement. By using cryptographic attestations such as Merkle trees and on-chain verification, exchanges can demonstrate that customer assets are actually backed without revealing individual balances.
The mechanics are straightforward: independent oracles like Chainlink fetch off-chain balance data, compare it against liabilities, and update PoR smart contracts when deviations occur. Decentralized applications can then audit reserves autonomously, rejecting under-collateralized transactions and greenlighting those that meet solvency thresholds.
Proof-of-Reserves process with Chainlink, smart contracts, and dApps (Source: ImmuneBytes)
Proof-of-Reserves uses oracles and Merkle trees to validate exchange solvency, triggering approvals or rejections when collateralization shifts.
Adoption, however, is inconsistent. As of mid-2024, only 47.3% of BTC held on exchanges was covered by verifiable PoR reports. Leaders set higher benchmarks: Gate.io maintains a reserve ratio of 128.6% through third-party audits, while Bitget publishes live dashboards showing ratios above 200%. For institutions, suSch transparency is now a baseline expectation.
Yet solvency is only one side of resilience. Exchanges must also prove they can continue operations under stress—whether from cloud outages, cyberattacks, or geopolitical disruption. This is where operational resilience frameworks come in, aligning with models like NIST CSF or the Bank of England’s resilience guidelines.

Operational resilience lifecycle including risk governance, continuity planning, and exit strategies (Source: Microsoft)
Operational resilience ensures exchanges can withstand cloud failures, systemic outages, or black swan events without halting user access.
In practice, this means:
- Business continuity planning for exchange infrastructure and critical service providers.
- Disaster recovery procedures with tested failover systems.
- Insurance pools like Binance’s SAFU, protecting users from catastrophic loss.
- Zero-day patching and monitoring, as seen in Microsoft Exchange Online’s updates, proving resilience requires continuous defense, not annual audits.
For institutional partners, the combination of PoR transparency + resilience frameworks is decisive. It shows not only that assets exist, but that users can always access them even under extreme market or technical stress.
Conclusion
Security is no longer a differentiator, it is the entry ticket. The five benchmarks CCSS, ISO/IEC 27001, FATF Travel Rule, API standards, and Proof-of-Reserves with resilience define the minimum threshold of trust for exchanges. Those that adopt and prove compliance gain credibility with regulators, institutions, and users. Those that don’t remain one incident away from collapse.
Explore how Twendee Labs empowers teams to architect resilient and compliant exchanges. Connect with us via LinkedIn or X.