Your smart contracts passed every audit. Your dApp still got hacked. This is not a hypothetical. It’s the defining pattern of Web3 security failures in 2024 and 2025. Developers pour resources into smart contract audits and attackers walk through the frontend door. If you’re building a decentralized application, the central question is no longer “is my contract bug-free?” It’s: is your entire architecture designed to survive adversarial conditions?
The Real Reason Web3 Gets Hacked
Most teams treat secure dApp development as a code review problem. Audit the contracts, ship the product, patch when needed. This model has cost the industry billions. According to CertiK’s Hack3d report, over $2.36 billion was lost across 760 on-chain security incidents in 2024, a 31.6% increase over 2023. (CertiK Hack3d 2024). More telling: phishing attacks and private key compromises, not smart contract bugs accounted for the top two loss vectors, totaling nearly $1.9 billion combined.
By 2025, the pattern had deepened. CertiK data shows 69% of crypto losses that year stemmed from wallet or infrastructure compromises rather than smart contract vulnerabilities. (Medium, Jan 2026). Access control failures alone accounted for 75% of all crypto hacks in 2024, per Hacken’s annual report. (Hacken 2024 Security Report). The uncomfortable truth: Web3 is being broken at the architecture level, not just the contract level.
When BadgerDAO lost $120M in 2021, the smart contracts were fine. Attackers stole a Cloudflare API key and injected malicious scripts into the frontend that tricked users into signing malicious transactions. (Extropy.IO on Medium). When Ambient Finance was hit in 2024, it was a DNS hijack, the contracts were never touched. When Bybit suffered the largest crypto theft in history ($1.49B), the root cause was access control and operational security failures, not a code bug. (Nadcab Labs, 2025)
Research from 2023 found that approximately 35% of crypto hacks involved off-chain vulnerabilities rather than smart contract exploits and that number has only grown. (Extropy.IO). This is the architecture problem. And it demands an architecture solution.
How to Build Secure dApps That Can Survive Attacks
Secure dApp development is not about eliminating every bug. It is about engineering systems that continue to protect assets even when something inevitably breaks. In 2024 alone, over $2.36 billion was lost across 760 on-chain incidents, marking a 31.6% increase year-over-year (CertiK Hack3d Report 2024: https://www.certik.com/resources/blog/hack3d-2024). The majority of these losses were not caused by exotic smart contract vulnerabilities, but by compromised keys, phishing campaigns, DNS hijacks, and infrastructure failures.
To build dApps that survive attacks, security must be embedded structurally across contracts, infrastructure, frontend, and operational governance. The following methods define how secure dApp development should be executed in practice.
1. Start With an Attack Surface Model, Not a Feature Roadmap
Most Web3 teams begin by defining tokenomics and product features. Secure dApp development begins differently with an attack surface model. Before writing code, teams should map every component that can influence fund movement: smart contracts, admin keys, treasury wallets, RPC endpoints, backend APIs, frontend hosting, DNS control, oracle integrations, cross-chain bridges, and CI/CD pipelines. Each of these elements represents a potential trust boundary.
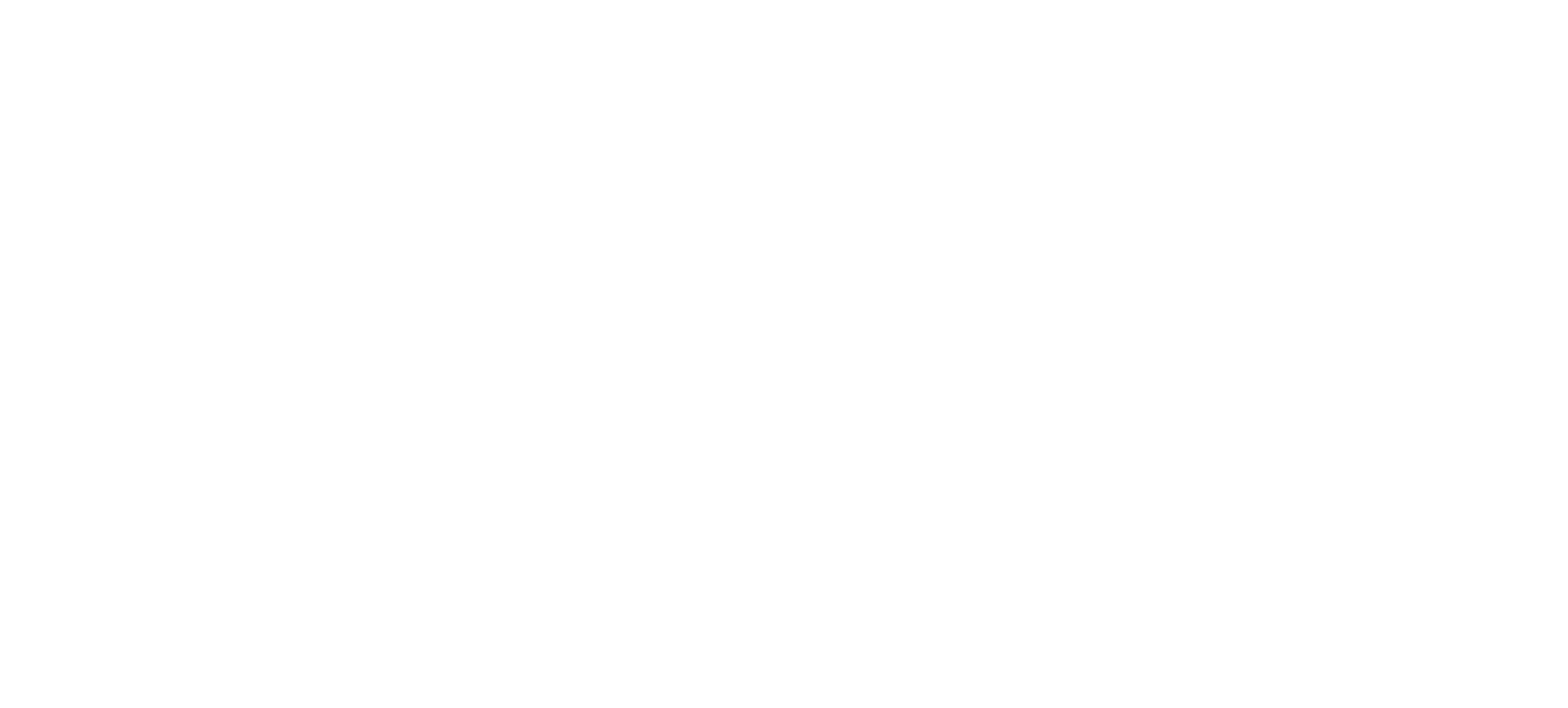
Web3 dApp architecture attack surface including frontend, provider and smart contracts (source: codluck)
Research from Extropy and security analysts has shown that roughly 35% of crypto hacks involve off-chain vectors rather than contract exploits. That percentage continues to grow as dApps become more modular and infrastructure-heavy. The key question is not “can this contract be exploited?” but “if this layer is compromised, what can an attacker do?”
Designing secure dApp development architecture means explicitly calculating blast radius. If a single compromised admin key can drain the treasury, architecture has failed even if the contract logic is flawless. Security begins by defining how much damage each component is allowed to cause.
2. Reduce On-Chain Complexity Before You Try to Secure It
Smart contracts are immutable and capital-exposed. Every additional line of on-chain logic expands permanent risk. Secure dApp development therefore starts by minimizing what truly needs to be on-chain. Business rules that do not require consensus should remain off-chain, where they can be updated and monitored. Upgradeable proxy patterns should be used cautiously, because they shift risk from logic bugs to governance control.
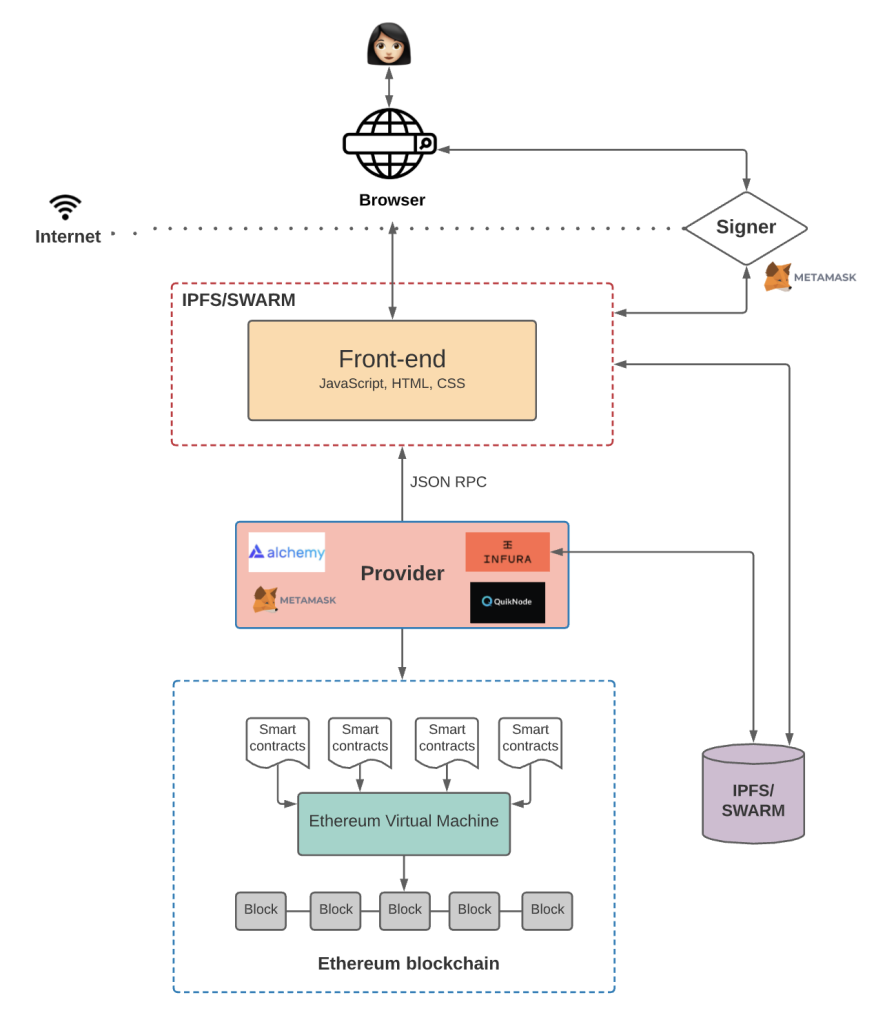
Layered Web3 development stack including UI, smart contracts, testing and audit (source: 57blocks)
The Parity Multisig incident froze over $150 million because a shared library contract was improperly initialized (technical breakdown: https://arxiv.org). The flaw itself was simple; the architectural coupling amplified its impact.
Reentrancy vulnerabilities remain a leading exploit vector despite being well documented for years. However, survivability goes beyond simply applying the Checks–Effects–Interactions pattern. It involves structuring contracts so that even if reentrancy occurs, withdrawal limits, delayed settlement mechanisms, or segmented treasuries prevent catastrophic loss.
In secure dApp development, complexity is treated as a liability. Reducing cross-contract dependencies and external call chains directly reduces the number of states attackers can manipulate.
3. Engineer Access Control as Critical Infrastructure
Access control failures are among the most damaging weaknesses in Web3. Hacken’s 2024 Security Report found that 75% of crypto-related hacks involved access control vulnerabilities (Hacken Report 2024: https://hacken.io/research/2024-report). That statistic reflects systemic architectural design flaws rather than isolated mistakes.
Secure dApp development treats privileged access as a form of critical infrastructure. Owner keys are not just administrative tools; they are treasury control mechanisms. Governance upgrade functions are not developer conveniences; they are potential single-transaction takeover vectors.
A resilient architecture separates deployer authority from treasury authority. It enforces multi-signature approval for upgrade paths. It introduces time-locks so that any governance change is observable before execution. It ensures no externally owned account has unilateral power over funds.
The largest crypto theft reported in 2025, involving Bybit’s $1.49B loss, stemmed from operational security and access control breakdowns rather than a flawed smart contract (industry coverage summary: https://medium.com). The lesson is clear: mathematically correct contracts cannot compensate for centralized control weaknesses.
Secure dApp development must assume privileged credentials will eventually be targeted. The architecture must prevent any single compromise from collapsing the system.
4. Treat Infrastructure as a First-Class Security Layer
Infrastructure compromises now account for a majority of crypto losses. CertiK reporting indicates that 69% of losses in 2025 were linked to wallet or infrastructure compromises rather than direct contract vulnerabilities (CertiK industry summary).
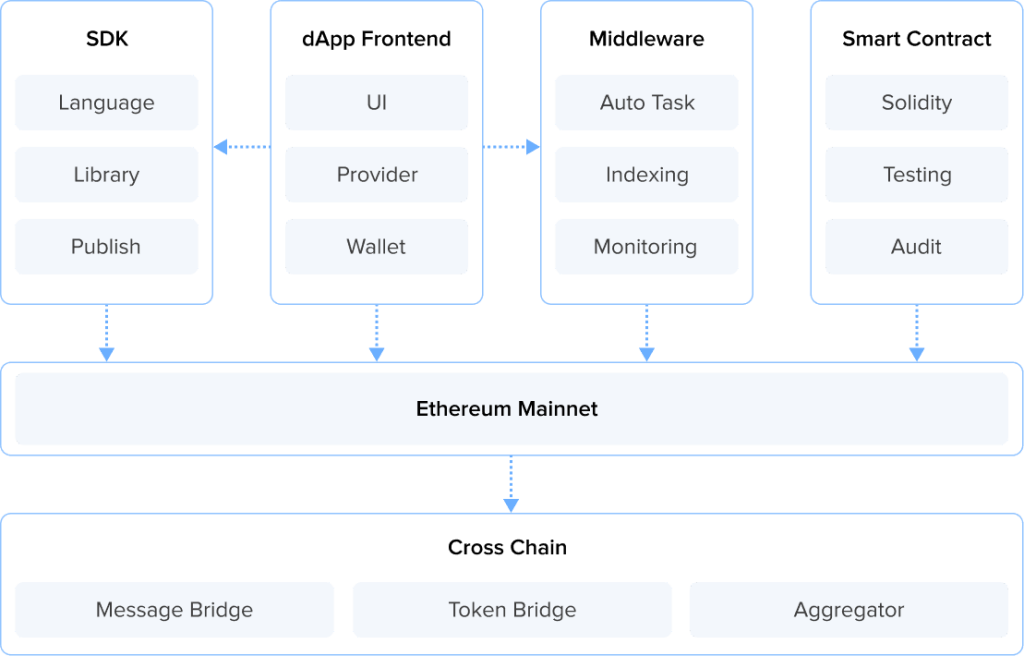
Web3 infrastructure flow including wallet, RPC provider, indexing and monitoring tools (source: 57blocks)
RPC endpoints, backend APIs, CI/CD pipelines, and dependency packages all influence how users interact with the blockchain. If RPC responses are manipulated, frontend displays can show a falsified state. If backend APIs are poorly validated, malicious input can trigger legitimate contract calls without exploiting Solidity itself.
In 2025, a supply-chain attack compromised 18 JavaScript packages with more than 2.6 billion weekly downloads, targeting Web3 applications and wallets. No contract exploit was required; dependency poisoning was sufficient. Secure dApp development therefore enforces least-privilege IAM across cloud infrastructure, isolates production keys from developer environments, validates RPC responses when feasible, and implements immutable logging mechanisms that attackers cannot silently modify. Infrastructure is not a supporting layer. It is an extension of the security perimeter.
5. Secure the Frontend Against Web2 Attack Patterns
Frontend compromise is one of the most underestimated risks in Web3. The BadgerDAO attack, which resulted in a $120M loss, was enabled through malicious script injection after attackers gained access to a Cloudflare API key (analysis reference: https://medium.com/extropy-io). The smart contracts were not the entry point. Secure dApp development addresses this by enforcing strict Content Security Policies, Subresource Integrity checks, and DNS monitoring. However, survivability also depends on transaction clarity. Users must be shown exactly what they are signing, including full approval scopes and recipient addresses. Transaction simulation prior to signature reduces the likelihood that altered frontend scripts can deceive users. Web3 inherits Web2’s attack surface. Ignoring that reality allows attackers to bypass audited contracts entirely.
6. Build Monitoring and Damage Containment Into the Core Architecture
No system can guarantee absolute prevention. Survivability depends on detection speed and containment strategy. The $2.36B lost in 2024 reflects not only vulnerabilities but delayed response windows (CertiK Hack3d Report 2024). When anomalous activity goes unnoticed, treasury drains accelerate.
Secure dApp development integrates real-time monitoring for unusual token movements, abnormal approval patterns, and unexpected contract interactions. Emergency pause mechanisms must exist before incidents occur. Withdrawal caps and segmented liquidity pools limit how much capital can be drained within a single transaction or epoch. The objective is not to eliminate every exploit. It is to ensure that when exploitation occurs, the loss is constrained and recoverable. Blast radius containment is what differentiates fragile dApps from resilient ones.
Structures Secure dApp Development in Practice
Designing survivable Web3 systems requires more than implementing isolated security controls. It demands architectural alignment across smart contracts, infrastructure, and user interaction layers from the outset.
At Twendee Labs, secure dApp development begins before implementation. Security modeling is conducted at the architecture stage, where trust boundaries, privilege levels, and potential blast radius are explicitly defined. This prevents security from becoming a reactive add-on later in the lifecycle.
- At the smart contract layer, the focus is on reducing structural exposure rather than patching vulnerabilities post-deployment. Attack surface is minimized, privileged operations are compartmentalized, and reentrancy protections and access control hierarchies are embedded into contract design. Independent audits and automated fuzz testing are integrated as validation mechanisms, not as substitutes for architectural rigor.
- At the infrastructure layer, API boundaries are treated as adversarial interfaces. Least-privilege IAM models, RPC redundancy, and immutable logging mechanisms are established to ensure that backend compromise does not silently escalate into fund-level risk. Dependency monitoring and supply-chain vigilance are incorporated into CI/CD workflows to mitigate indirect exposure.
- At the frontend layer, protections extend beyond interface polish. Content Security Policies, Subresource Integrity validation, DNS monitoring, and transaction simulation mechanisms are embedded to prevent user-facing manipulation that could bypass contract correctness entirely.
Security is not treated as the final milestone before launch. It defines how every system component is structured from day one.
Conclusion
Secure dApp development is not a checklist and not a single audit milestone. It is a layered architectural discipline spanning smart contracts, infrastructure, frontend security, runtime monitoring, and blast-radius containment. The data from 2024 and 2025 demonstrates a consistent pattern: architecture failures, access control weaknesses, and off-chain vulnerabilities account for the majority of catastrophic losses.
Building dApps that survive attacks means designing for adversarial conditions from the first architectural decision. For teams looking to architect Web3 products with security-by-design across contract logic, infrastructure, and frontend layers, explore how Twendee Labs approaches secure dApp development and connect with the team to discuss building systems engineered to withstand real-world attack conditions.
Contact us: Twitter & LinkedIn Page
Read latest blog: Building a Tokenized Asset Platform: Core Requirements in 2025